Vault7: CIA Hacking Tools Revealed

Navigation: » Latest version
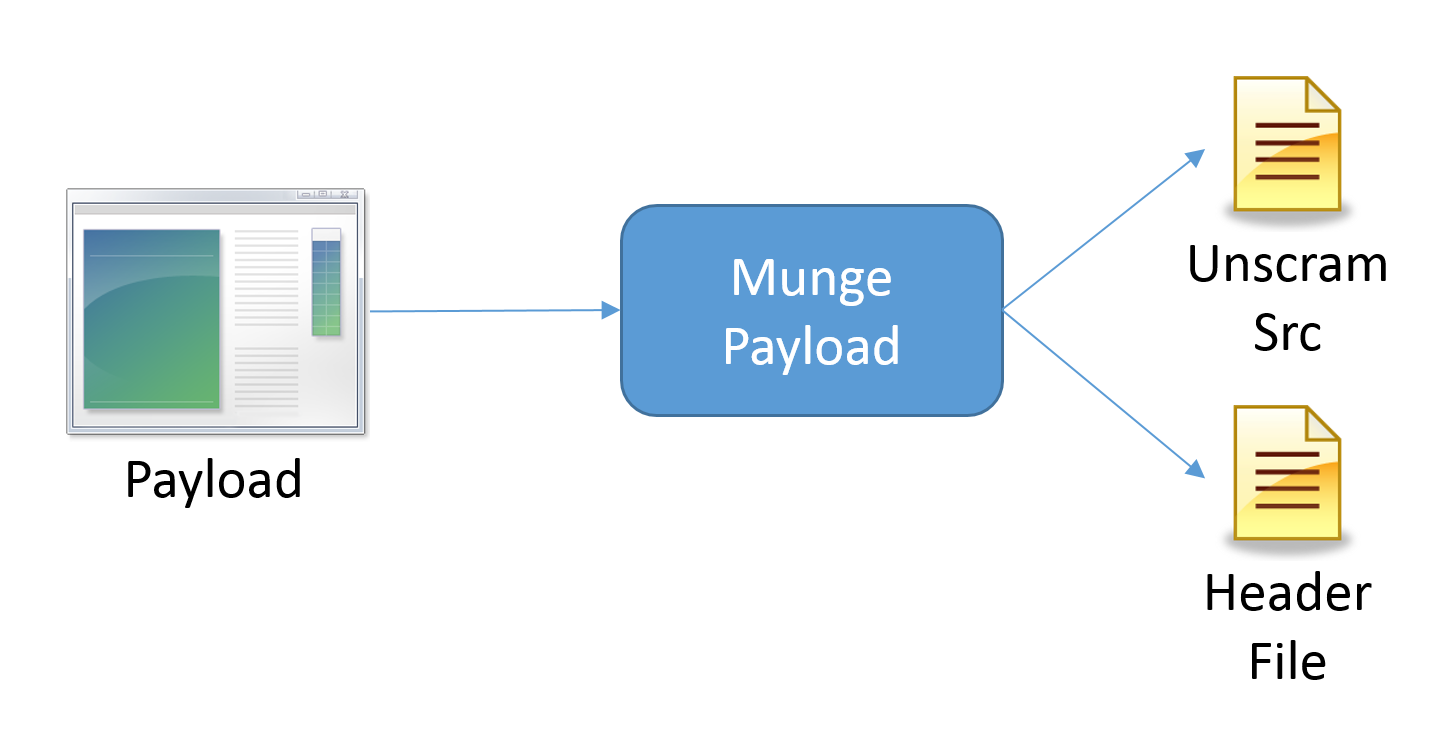
Munge Payload
SECRET//NOFORN
Munge Payload
Description:
The Munge Payload utility is designed to help automate some of the steps in obfuscating or encrypting embedded payloads.Specifically, Munge Payload is currently capable of supporting the Melomy style of embedding/trojaning. The utility will read in a payload, modify it (or won't) with the specified parameters, and generate a formatted header file with an array containing the payload. The currently supported modifications to the payload are: None, XOR Rolling XOR (RXOR), Compression (ZLIB), AESAdvanced Encryption Standard Encryption, Public/Private Key Encryption, or a combination of these. Currently, the utility will overwrite the header file you specify if it already exists. The tool also generates the deobfuscation/decryption code needed to repair the payload during execution. The order of manipulation if all options are specified is: Compression, XOR, Rolling XOR, AESAdvanced Encryption Standard Encrypt (MSFT_AES_256), Public/Private Encrypt (MSFT_RSA_4096).
AES Key FIle Generation: Create a text file -> Open in WinHex -> Resize to 32 bytes -> Edit -> Fill FIle -> Cryptographically secure data
RSA (Pub/Priv) Key File Generation: Use KeyGenerator.exe (see repository MungePayload folder) -> Generates privateKey.pem and publicKey.pem
Files generated by Munge Payload:
- Unscram.txt - Dropped in current directory. Contains unscramble source to de-obfuscate the payload
- Payload.munge - The obfuscated copy of the payload is dropped in the current directory
- Header file - Replaced in place or creates in at the location specified
Design:
Examples:
Usage:
('section' missing)
No Obfuscation:
('section' missing)
XOR:
('section' missing)
RXOR:
('section' missing)
Compression:
AES:
RSA (Pub/Priv):
Combo - Compress, XOR, AES:
Combo - All (just for fun):
Stash Repository: Munge Payload Repository
Change Log:
('excerpt' missing)
SECRET//NOFORN